Protection of Information Assets
About this Course
This course offers an in-depth exploration of information security auditing principles, tailored for professionals preparing for the CISA certification. Starting with an overview of frameworks, standards, and guidelines, you will understand their critical role in protecting information assets. The course outlines the responsibilities of IS auditors in evaluating security baselines and implementing effective data privacy practices. Key modules focus on physical and environmental controls, ensuring that you are equipped to audit diverse aspects of information systems security, from infrastructure protection to compliance requirements. As you progress, the course delves into access management and data protection strategies. You will learn about identity and access management principles, logical access controls, and common authorization issues that pose risks to information systems. Detailed discussions on audit logging, data loss prevention (DLP), and network infrastructure will provide you with the skills needed to monitor and protect sensitive information effectively. The course also addresses the auditing of applications within networked environments, helping you understand the complexities of securing interconnected systems. In the latter sections, the focus shifts to advanced topics such as cryptography, network security, and cloud computing. You will explore the fundamentals of encryption systems, including symmetric and asymmetric keys, and learn to apply cryptographic principles for robust information security. Modules on PKI, virtualization, and cloud environments will further enhance your ability to assess and mitigate risks in modern IT landscapes. Additionally, the course covers security testing techniques, network penetration testing, and the use of IDS/IPS tools, preparing you to perform comprehensive security audits. By the end of this course, you will have a solid understanding of information security auditing, ready to tackle the CISA exam and advance your career in cybersecurity. This course is designed for IT auditors, security professionals, and individuals preparing for the CISA certification. It is suitable for those with a basic understanding of information systems and security principles. No prior CISA experience is required, but familiarity with IT audit processes will be beneficial.Created by: Packt

Related Online Courses
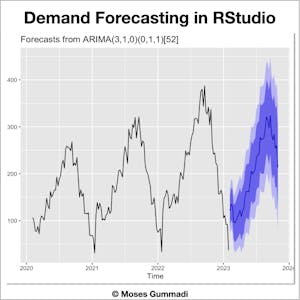
This Guided Project Demand Planning in RStudio: Create Demand Forecast is for Supply Chain and/or Operations Analysts. In this 2-hour long project-based course, you will learn how: - Analyse demand... more
By the end of this course, you will understand the test-driven development process in Java at a beginner\'s level.Created by: Coursera Project Network more
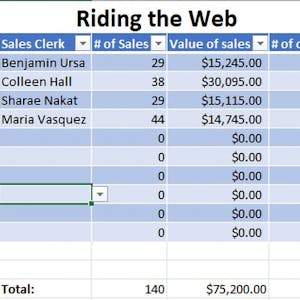
Microsoft Excel has a wide array of versatility and application across countless industries. However, it can be very particular in how the formulas need to be written to reference images, cells,... more
Students want to be successful when they embark on a learning journey. That success is dependent on a constellation of factors: 1) they need to be able to process the material that is presented in... more
\"Introduction to Fluent Assertions\" is a detailed course designed to provide .NET developers with a thorough understanding of Fluent Assertions, a library that enhances the clarity and... more